routers
US
・UK
A1
n. pl.Noun (plural)
Video subtitles
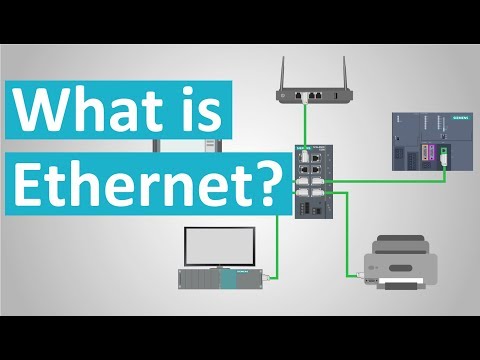
What is Ethernet?
- Switches and routers that act as the director of the network and connect multiple computers or even networks together to enable communication between all the different devices.
Switches and routers that act as the director of the network and connect multiple computers or even networks together to enable communication between all the different devices.
- “Switches” and “Routers” that act as the director of the network
“Switches” and “Routers” that act as the director of the network
Connecting Mobile Devices - CompTIA A+ 220-1101 - 1.3
- You can probably still find devices in your infrastructure that use DB9 connections with RS-232 to be able to connect and view consoles on switches, routers, and other devices.
You can probably still find devices in your infrastructure that use DB9 connections with RS-232 to be able to connect and view consoles on switches, routers, and other devices.
- You can probably still find devices in your infrastructure that use DB9 connections with RS232 to be able to connect and view consoles on switches, routers, and
You can probably still find devices in your infrastructure that use DB9 connections with RS232 to be able to connect and view consoles on switches, routers, and
WWDC 2019 Keynote Apple
- And so we're bringing HomeKit to routers.
And so we're bringing HomeKit to routers.
- The first HomeKit-enabled routers will be coming from Linksys, Eero, and internet service providers like Charter Spectrum.
The first HomeKit-enabled routers will be coming from Linksys, Eero, and internet service providers like Charter Spectrum.
Sell Your Ideas the Steve Jobs Way
- Cisco makes big routers and switches that nobody ever sees.
Cisco makes big routers and switches that nobody ever sees.
- Cisco makes big routers and switches that nobody ever sees so they've become
Cisco makes big routers and switches that nobody ever sees so they've become
What is Net Neutrality and why is it important? [Full Video - Multilanguage Subs]
- On the crossroads of these streets are routers, which direct the data packets on the right route to their destination.
On the crossroads of these streets are routers, which direct the data packets on the right route to their destination.
- The routers don't care who comes down the road, nor do they care how they look, where they are from, where they want to go, or what content they have with them.
The routers don't care who comes down the road, nor do they care how they look, where they are from, where they want to go, or what content they have with them.
AirBnB in Tokyo | 東京での宿泊
- Another good thing about Airbnbs in Japan is that a lot of them are equipped with free internet, um, portable Wi-Fi, um, routers.
Another good thing about Airbnbs in Japan is that a lot of them are equipped with free internet, um, portable Wi-Fi, um, routers.
- Another good thing about Airbnbs in Japan is that a lot of them are equipped with free internet, portable Wi-Fi routers.
Another good thing about Airbnbs in Japan is that a lot of them are equipped with free internet, portable Wi-Fi routers.
SANS Stormcast Friday, April 18th: Remnux Cloud Environment; Erlang/OTP SSH Vuln; Brickstorm Ba…
- hello and welcome to the friday april 18th 2025 edition of the sands internet storm centers stormcast my name is johannes ulrich and today i'm recording from orlando florida today we got another guest diary by one of our undergraduate interns jacob clay camp did write about how to get started in malibu analysis of course we have plenty of diaries always about malibu analysis didier and xavier most notably are heavily contributing to this this is more the beginners view of malibu analysis and sort of how to get started with malibu analysis using a cloud-based system a couple interesting parts here first of all jacob is using aws a free instance and then uses chasm workspaces in order to essentially get a remote desktop into a container which then runs remnux this is lenny seltzer's reverse analysis environment all of this is linux-based and since it is set up in a container it's also easy to reset and the cloud deployment of course makes it nice and isolated from anything that you may have going on in your home network overall interesting setup and then jacob is going over a quick analysis of a red tail sample and how to apply this particular environment to the analysis of this particular matter interesting a write-up and nice step-by-step guide to help you get started and then we have a critical vulnerability affecting the erlang otp ssh library this affects any ssh servers written in this language the vulnerability was found by researchers at the ruhr university city in bochum now the otp here in erlang otp does not stand for one term one-time password instead it does stand for the open telecom platform this particular version of erlang was created and maintained initially by ericsson and is often used in telecom related devices routers and the like so certainly there is quite a number of affected devices out there the cbss score of the vulnerability is a perfect 10.0 because it does allow for arbitrary code execution without authentication the problem is that some ssh messages some ssh protocol messages can be sent and executed before authentication finishes due to this bug and that then leads to execution now the user this this code executes at depends on the user the ssh server is running at at the time it receives these messages definitely upgrade but of course since this is a vulnerability in the library used to create the ssh server you may have to wait for respective vendors to actually release updates here in the meantime the only alternative you have is to disable or firewall the ssh server and belgium security company inviso did release a report with details regarding some of their recent findings of the brickstorm backdoor brickstorm has been used in linux in in sort of vmware environments but now they also found a version of this backdoor on windows there are a couple interesting things to note here unlike most backdoors this backdoor actually does not have a remote code execution capability they say that typically rdp and such is used instead by the attacker and that they specifically didn't include a remote code execution capability to evade some heuristic and behavioral detection that you often find that would flag any code execution behavior instead this particular backdoor is able to read write files from the file system it also has some network components that would allow an attacker to essentially use an affected system as a pivot to scan other systems in the network so certainly a capable piece of malware also interesting as a command control channel they're using cloud flare workers and similar systems that again are less likely going to trigger alerts interesting report and it also includes some good indicators of compromise and the ways and techniques how you can actually find if you are affected by this particular backdoor and openai released its latest greatest model gpt 4.1 but this didn't happen amid some controversy around the security aspects here first of all this model was released without the usual safety reports or system cards which typically outline how this particular model was created to be safe meaning not for example allowing to create malware and apparently some of these safeguards that you often find in these models are missing from gpt 4.1 making it trivial to create malware with this model interesting problem here and not even sure if this will be something that the openai will fix in short notice but definitely we have seen malicious models of course before but not from major vendors like openai well that is it for today so thanks again for listening and thanks everybody who i met here i mean all of you listeners at the event here in orlando and well i'll talk to you again on monday bye
hello and welcome to the friday april 18th 2025 edition of the sands internet storm centers stormcast my name is johannes ulrich and today i'm recording from orlando florida today we got another guest diary by one of our undergraduate interns jacob clay camp did write about how to get started in malibu analysis of course we have plenty of diaries always about malibu analysis didier and xavier most notably are heavily contributing to this this is more the beginners view of malibu analysis and sort of how to get started with malibu analysis using a cloud-based system a couple interesting parts here first of all jacob is using aws a free instance and then uses chasm workspaces in order to essentially get a remote desktop into a container which then runs remnux this is lenny seltzer's reverse analysis environment all of this is linux-based and since it is set up in a container it's also easy to reset and the cloud deployment of course makes it nice and isolated from anything that you may have going on in your home network overall interesting setup and then jacob is going over a quick analysis of a red tail sample and how to apply this particular environment to the analysis of this particular matter interesting a write-up and nice step-by-step guide to help you get started and then we have a critical vulnerability affecting the erlang otp ssh library this affects any ssh servers written in this language the vulnerability was found by researchers at the ruhr university city in bochum now the otp here in erlang otp does not stand for one term one-time password instead it does stand for the open telecom platform this particular version of erlang was created and maintained initially by ericsson and is often used in telecom related devices routers and the like so certainly there is quite a number of affected devices out there the cbss score of the vulnerability is a perfect 10.0 because it does allow for arbitrary code execution without authentication the problem is that some ssh messages some ssh protocol messages can be sent and executed before authentication finishes due to this bug and that then leads to execution now the user this this code executes at depends on the user the ssh server is running at at the time it receives these messages definitely upgrade but of course since this is a vulnerability in the library used to create the ssh server you may have to wait for respective vendors to actually release updates here in the meantime the only alternative you have is to disable or firewall the ssh server and belgium security company inviso did release a report with details regarding some of their recent findings of the brickstorm backdoor brickstorm has been used in linux in in sort of vmware environments but now they also found a version of this backdoor on windows there are a couple interesting things to note here unlike most backdoors this backdoor actually does not have a remote code execution capability they say that typically rdp and such is used instead by the attacker and that they specifically didn't include a remote code execution capability to evade some heuristic and behavioral detection that you often find that would flag any code execution behavior instead this particular backdoor is able to read write files from the file system it also has some network components that would allow an attacker to essentially use an affected system as a pivot to scan other systems in the network so certainly a capable piece of malware also interesting as a command control channel they're using cloud flare workers and similar systems that again are less likely going to trigger alerts interesting report and it also includes some good indicators of compromise and the ways and techniques how you can actually find if you are affected by this particular backdoor and openai released its latest greatest model gpt 4.1 but this didn't happen amid some controversy around the security aspects here first of all this model was released without the usual safety reports or system cards which typically outline how this particular model was created to be safe meaning not for example allowing to create malware and apparently some of these safeguards that you often find in these models are missing from gpt 4.1 making it trivial to create malware with this model interesting problem here and not even sure if this will be something that the openai will fix in short notice but definitely we have seen malicious models of course before but not from major vendors like openai well that is it for today so thanks again for listening and thanks everybody who i met here i mean all of you listeners at the event here in orlando and well i'll talk to you again on monday bye
- This particular version of Erlang was created and maintained initially by Ericsson and is often used in telecom-related devices, routers, and
This particular version of Erlang was created and maintained initially by Ericsson and is often used in telecom-related devices, routers, and
Marc Andreessen on Big Breakthrough Ideas and Courageous Entrepreneurs
- It's like, okay, like, for example, for networking, you'd have, like, you know, fiber optics and communication chips that then lead into things like routers, um, that then lead into things like, you know, ISPs and then ultimately lead into things like, um, you know, other, you know, wireless businesses or whatever.
It's like, okay, like, for example, for networking, you'd have, like, you know, fiber optics and communication chips that then lead into things like routers, um, that then lead into things like, you know, ISPs and then ultimately lead into things like, um, you know, other, you know, wireless businesses or whatever.
- fiber optics and communication chips, the family of such things like routers,
fiber optics and communication chips, the family of such things like routers,
Brian May - Classic Rock Interview - Part 2
- The first is to use a vulnerability in the default security setup in almost all routers built between 2009 and 2012.
The first is to use a vulnerability in the default security setup in almost all routers built between 2009 and 2012.
- in almost all routers built between 2009 and 2012.
in almost all routers built between 2009 and 2012.
Walter Isaacson: "The Innovators" | Talks at Google
- We call them we basically call them routers now.
We call them we basically call them routers now.
- We knew about, you know, putting we didn't call them routers then.
We knew about, you know, putting we didn't call them routers then.



![What is Net Neutrality and why is it important? [Full Video - Multilanguage Subs]](https://img.youtube.com/vi/HCUg5A-ZAw0/hqdefault.jpg)